Telcos across markets are called upon to strengthen their privacy protection standards in the wake of increasing legal compliance burden and customer awareness
In most developed nations, privacy – both information and data are regulated by law. Many countries have specific privacy acts that regulate how government and private organizations collect, use/process and disclose personal information. These laws also provide individuals with the right to access the information about them that is stored by organizations and the right to request that any erroneous information be corrected.
Unlawful storage of personal data, storage of inaccurate personal data and the abuse or unauthorized disclosure of such data is considered a violation of privacy in some European countries and the United States. User awareness around privacy is ver y high in these countries. In 2010
Google had to turn in/off Wi-Fi data collected by its Street View cars after privacy concerns were raised in Germany and some other countries. While it is considered perfectly normal in some countries like India for someone to ask for another person’s salary, date of bir th and other such personal information, such questions would be completely outside the boundaries of propriety, and the law, in many Western countries.
This paper dwells upon some fundamental issues around privacy and takes a look at the telecom sector as a specific case. However, the essence of the discussion here applies to most other sectors.
Personal information or personally identifiable information (PII) is something that helps to identify an individual or directly points to a person’s attributes. This ‘something’ may be a telephone number or an email address or anything apar t from the obvious name of the individual. So, first and foremost, it is necessar y to define what constitutes the PII of an individual – a consumer, an employee, a contractor associated with your organization, or anyone else.
Next, privacy requirements should cover information and data. Information and data are frequently used interchangeably. Information denotes processed data and hence is more clear, useful and contextual. Data is the raw element lying in the technology system (it could be anywhere) which requires crunching to make it more meaningful and actionable. Therefore, an information privacy program would cover the entire information management system and communication channels, with data protection treatment within the technology ecosystem. As a matter of fact, we often see that organizations have multiple policies – information security policy, information privacy policy and online privacy policy – to cover all possible avenues of privacy treatment.
Privacy vs. Confidentiality
There are two schools of thought here. First, privacy is covered under the confidentiality aspect of the security triad and is governed by the classification of information. This makes confidentiality a bigger umbrella under which privacy requirements are addressed and remains the responsibility of the chief security officer.
The second school of thought suggests that confidentiality is an extension of privacy. This school argues for protecting identifiable private information by making its access and disclosure strictly governed by an agreement with the person whose information is involved. In other words, privacy concerns people (right to personal information) and confidentiality concerns data (the way secrecy of personal information is managed). Thus, in some organizations a separate position is established for dealing with privacy – to super vise the application of the privacy policy against a continuously changing regulator y landscape.
Indian Telecom Scenario
The Indian telecom industr y is being discussed here as it has been the fastest growing industry in India over the last decade, and has attained maturity, alignment with global practices and regulator y compliance ver y quickly.
The Approach
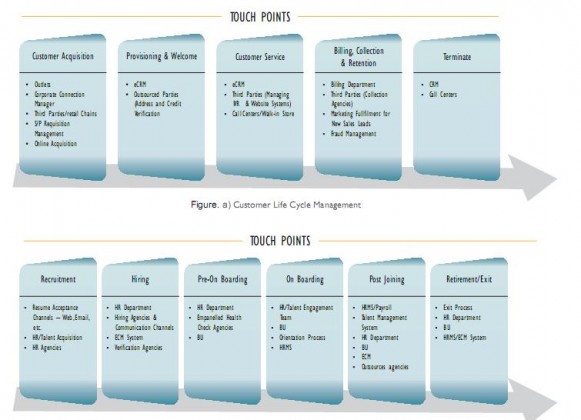
The shor t answer is a risk-based approach to do an impact assessment. Essentially there are four critical things to do. 1) It is impor tant to define the privacy and PII elements as well as to identify the drivers. 2) Create the PII inventor y to map business processes and underlying applications and infrastructure 3) Carr y out an impact assessment and determine critical processes, their boundaries and touch points. This assessment will enable to assess and refine the existing controls and to determine the level of protection required. 4) Enforcement through policy and framework to comply with the impacting regulation will remain central to the solutions approach.
The Challenge
Implementing the appropriate enterprise-wide privacy framework and adopting the right technology are critical. For example, initially it is necessar y to discover the PII data within the systems and then build the technical options for data protection. Other areas that are equally demanding are user awareness and training as well as privacy enhancing technologies that provide a degree of anonymity (which in turn help build trust and reduce risks), and monitoring and repor ting violations. At a higher level, end-user entitlements, data storage at rest and in transit, and third-par ty agreements driven through the procurement and vendor relationship cells should not be overlooked.
Conclusion
Maintaining privacy and protecting customer and employee personal information is a risk-management issue for all organizations. It goes beyond the regulator y requirements because customers expect their data to be protected to avoid identity thefts; it impacts an organization’s reputation and leads to financial loss due to lost revenue and litigation. Above all, customer confidence in the brand is impacted if there is no framework to deal with customer privacy.
By Manohar Ganshani, head Governance Risk & Compliance Practice, Wipro Consulting Services